FGNH is a record encoding ransomware contamination that confines admittance to information (reports, pictures, recordings) by scrambling documents with the “.fgnh” expansion. This guide shows you how to Remove FGNH Ransomware infection for nothing by adhering to simple task by-step directions.
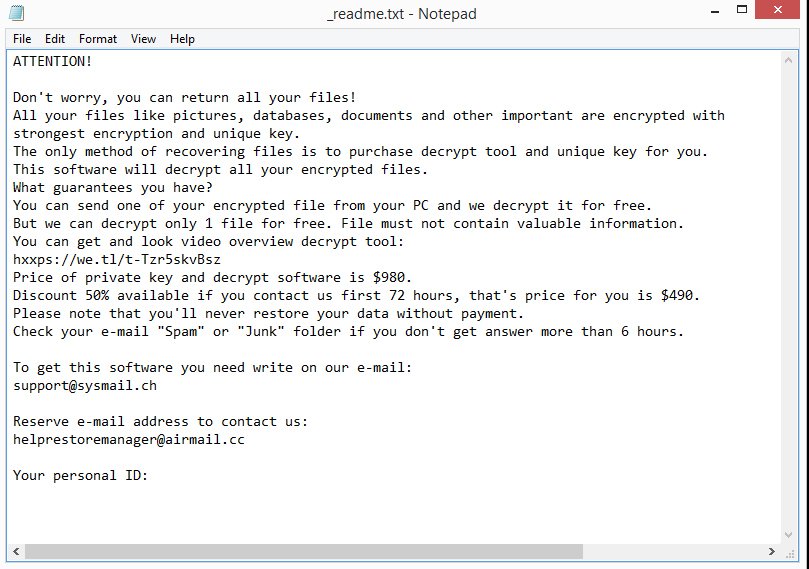
FGNH ransomware is a virtual extortion tool. It encodes documents with strong calculations that are normally used to get military-grade privileged insights. The message in Install Add Google Drive to File Explorer note recommends that casualty needs to contact ransomware operators in something like 72 hours to get a “rebate” on the decoding programming cost. On the off chance that the casualty does as such, the hoodlums set the payment add up to $490.
Fgnh is ordered by our malware research group as the DJVU ransomware contamination. One more variations of this family is Vgui, Fgui, Jjtt, and some others. There are sure scanners that overlook it as well as consequently letting its irruption. In reality, we need to call it that, as a result. Remove FGNH Ransomware” expansion that it adds toward the finish of your reports.
Fgnh contamination attacks your PC through secrecy and skill too. From that point onward, when entered it utilizes AES or RSA encryption calculations to lock your documents.
The evacuation of Fgnh ransomware is the primary thing that clients should execute to forestall further record encryption. Along these lines, we are offering methodology on this page containing segments for Removal Guide, conceivable Remove FGNH Ransomware of scrambled records, Ways to Protect the Computer.
What is the FGNH ransomware?
FGNH is a record scrambling ransomware disease that confines admittance to information (reports, pictures, recordings) by encoding documents with the “.Remove FGNH Ransomware” expansion. It then, at that point, endeavors to extort cash from casualties by requesting “emancipate”, as Bitcoin cryptocurrency, in return for admittance to information.
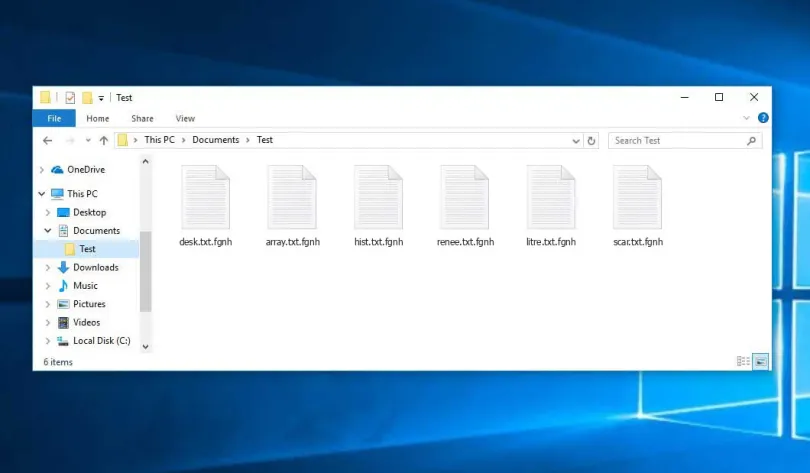
At the point when you are first tainted with the FGNH ransomware it will filter your PC for pictures, recordings, and significant efficiency archives and documents, for example, .doc, .docx, .xls, .pdf. At the point when these records are distinguished, the ransomware will encode them and change their augmentation to “.fgnh”, so you are as of now not ready to be open them.
When the FGNH ransomware has encoded the records on your PC, it will show the “_readme.txt” document that contains the payment note and directions on how to contact the writers of this ransomware. The casualties of this ransomware will be approached to contact these malware designers by means of the [email protected] and [email protected] email addresses.
How did the FGNH ransomware get on my computer?
The Remove FGNH Ransomware is dispersed through spam email containing tainted connections or by taking advantage of weaknesses in the working framework and introduced programs.
This is the way the FGNH ransomware could get on your PC:
- Cfhkf-hoodlums spam out an email, with manufactured header data, fooling you into accepting that it is from a transportation organization like DHL or FedEx. The email lets you know that they attempted to convey a bundle to you, yet fizzled for reasons unknown. At times the messages guarantee to be warnings of a shipment you have made. One way or the other, you can’t avoid being interested concerning what the email is alluding to – and open the connected record (or snap on a connection inside the email). Also, with that, your PC is contaminated with the FGNH ransomware.
- The FGNH ransomware was likewise noticed going after casualties by taking advantage of weaknesses in the program introduced on the PC or the working framework itself. Ordinarily took advantage of programming incorporates the working framework itself, programs, Microsoft Office, and outsider applications.
Fgnh ransomware infections and more
The primary direct in which the Remove FGNH Ransomware spread is in all likelihood achieves by means of phishing email crusade. This email fills in as the transporter of the dangerous infection or at times connects that opens up the program pages to a pernicious site where Fgnh ransomware can be infused straightforwardly to the PC.
Another justification for why Fgnh ransomware have outcome in penetrating the PC is because of the attachment to certain clients to broke programming or freeware installers. These applications are somehow being used by programmers to send Fgnh ransomware. During the arrangement, there will be no sign on the introduction being done by the Fgnh infection since running a careful attack was planned.
Social designing effort, web injectors, questionable ads, and dubious sites may not pull off similar amount of assaults as the ones above. Consequently, these techniques are still wellsprings of Remove FGNH Ransomware and different variations as Fgui, Eucy, and Ckae. Hence, web clients are encouraged to avoid these additional foundations of disease.