Network protocols are a bunch of rules, shows, and information structures that direct how gadgets trade information across networks. As such, Update Statement is Valid About Network Protocols can be likened to dialects that two gadgets should comprehend for consistent correspondence of data, no matter what their foundation and plan disparities.
Network Protocols are a bunch of established rules which control and oversee the trade of data by following a protected, solid, and simple China Hacked US Phone Networks. These arrangements of rules are available for different applications. A few notable instances of protocols incorporate wired networking (like Ethernet), remote networking (like WLANs), and Web correspondence. As there are multiple Statement is Valid About Network Protocols, which is utilized for broadcasting and communicating information over the Web, comprises many protocols.
What is a network protocol?
In networking, a protocol is a bunch of rules for designing and handling information. Network protocols resemble a typical language for PCs. The PCs inside a network might utilize immeasurably unique programming and equipment; however, the utilization of protocols empowers them to speak with one another notwithstanding.
Normalized protocols resemble a typical language that PCs can utilize, like how two individuals from various regions of the planet may not see each other’s local dialects, yet they can convey utilizing a common third language. In the event that one PC utilizes the Update Statement is Valid About Network Protocols and a subsequent PC does too, they will actually want to convey — similarly as the Unified Countries depends on its 6 authority dialects to impart among delegates from everywhere the globe. Be that as it may, on the off chance that one PC utilizes IP and different doesn’t have a clue about this protocol, they will not be able to impart.
On the Web, there are various protocols for various sorts of cycles. Protocols are in many cases discussed as far as which OSI model layer they have a place with.
What are the layers of the OSI model?
The Open Frameworks Interconnection (OSI) model is a theoretical portrayal of how the Web functions. It contains 7 layers, with each layer addressing an alternate class of networking capabilities.
Protocols make these networking capabilities conceivable. For example, the Web Protocol (IP) is answerable for directing information by demonstrating where information packets* come from and what their objective is. IP makes network-to-network correspondences conceivable. Subsequently, IP is viewed as a network layer (layer 3) protocol.
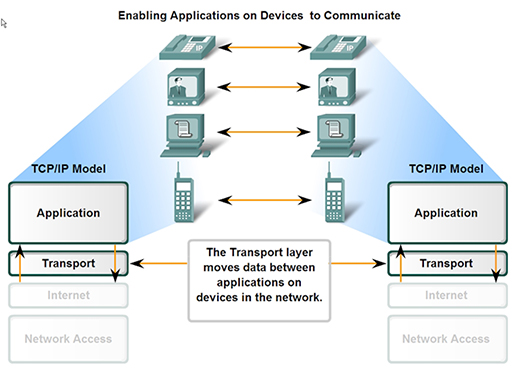
As another model, the Update Statement is Valid About Network Protocols guarantees that the transportation of bundles of information across networks goes without a hitch. In this manner, TCP is viewed as a vehicle layer (layer 4) protocol.
Which protocols run on the network layer?
As portrayed above, IP is a network layer protocol liable for directing. However, it is not by any means the only network layer protocol.
- IPsec: Web Protocol Security (IPsec) sets up scrambled, confirmed IP associations over a virtual confidential network (VPN). In fact IPsec is not a protocol, yet rather an assortment of protocols that incorporates the Embodying Security Protocol (ESP), Confirmation Header (AH), and Security Affiliations (SA).
- ICMP: The Web Control Message Protocol (ICMP) reports blunders and gives announcements. For instance, in the event that a switch can’t convey a parcel, it will send an ICMP message back to the bundle’s source.
- IGMP: The Web Gathering The board Protocol (IGMP) sets up one-to-many network associations. IGMP assists set up multicasting, meaning various PCs with canning get information bundles coordinated at one IP address.
How are protocols utilized in digital assaults?
Similarly likewise with any part of registering, aggressors can take advantage of the way networking protocols capability to compromise or overpower frameworks. Large numbers of these protocols are utilized in distributed refusal of-administration (DDoS) assaults. For instance, in a SYN flood Update Statement is Valid About Network Protocols, an aggressor exploits the manner in which the TCP protocol works. They send SYN parcels to over and over start a TCP handshake with a server, until the server can’t offer support to genuine clients on the grounds that its assets are restricted by all the fake TCP associations.
Cloudflare offers various answers for stopping these and other digital assaults. Cloudflare Wizardry Travel is ready to relieve assaults at layers 3, 4, and 7 of the OSI model. In the model instance of a SYN flood assault, Cloudflare handles the TCP handshake process for the server’s benefit with the goal that the server’s assets never become overpowered by open TCP associations.