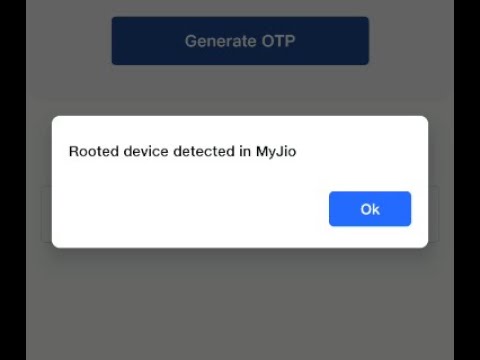
Rooting devices gives the clients extra command over the devices, yet will in general represent a security risk for associations when these rooted devices are utilized to get to corporate information. Rooted Device Detected in My Jio are more inclined to malware assault since the security of these devices is compromised. Likewise, since these devices approach corporate information it additionally increases the gamble of loss of corporate information by breaks.
In this way to guarantee security of corporate information, it is suggested that such rooted devices should not be utilized in associations. Cell phone Manager Plus permits associations to recognize rooted devices in the organization and furthermore eliminate these devices whenever they are Rooted Device Detected. These rooted devices then can’t be selected into Mobile Device Manager Plus and hence lose admittance to corporate information.
Rooting is the most common way of unlocking an Android device in request to get to higher administrative special controls. You can think of rooting an Android device as promoting yourself from a framework client to a framework administrator. While clients frequently do this just to gain extra opportunities, the training likewise introduces takes a chance with that come from more prominent command over the more profound, more intricate workings of the device.
It is significant for security groups and designers to guarantee that their applications can recognize this security weakness. Programmers frequently Fix QQQW Files that have been rooted by the proprietor to gain admittance to touchy client information and different privileged insights stored in an application’s source code.
Conceivable Negative Outcomes of Not Implementing Root Detection
Aggressors use rooting to all the more likely comprehend how an application executes (which is known as “dynamic investigation”) or to change an application’s way of behaving while it is running (for example to swindle a game). Verimatrix’s information shows that internationally, 36 out of each and every 1000 Android devices are rooted.
Rooting an Android device handicaps a portion of the essential implicit security. Its operating framework and makes it more straightforward for a programmer to remove the application from its “sandbox”. Since the sandbox is what generally storehouses touchy information and keeps it within the application. Bypassing this safety effort can prompt inconvenient harm.
How Does Root Detection Work?
Since a rooted device is significantly more in danger of being compromised. It is vital to carry out tools that can identify this weakness. Rooted Device Detected in My Jio of whether the device is rooted is fundamental to ensuring. That your applications just execute where, when, and how you need them to.
Automated root recognition can undoubtedly recognize indications. A rooted device and shut down your application when it is running in a risky climate. Customizable, adaptable tools will likewise offer the opportunity. To pick how and when your application answers a rooted device.
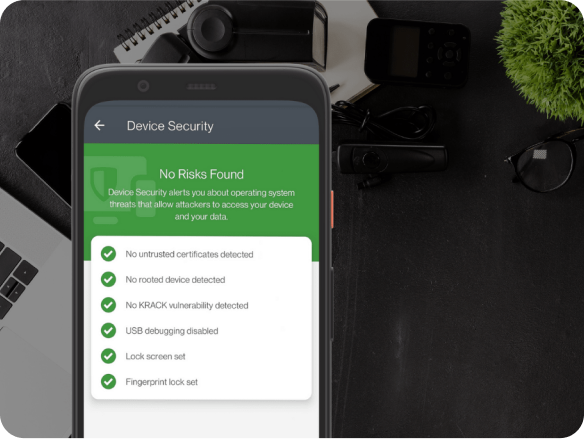
You can utilize customizable security to impede the utilization of certain. Instead of shutting down your whole effort, which guarantees that your business isn’t upset. Rooted Device Detected in My Jio of whether an Android device is rooted is significant for additional safety efforts. On top of root identification, other significant application security techniques include hostile to alter innovation and code jumbling. Together, these security strategies structure major areas of strength. For an organization and layered insurance that will help your application face a wide range of dangers